Basic Pentesting Vulnhub
Reconnaissance
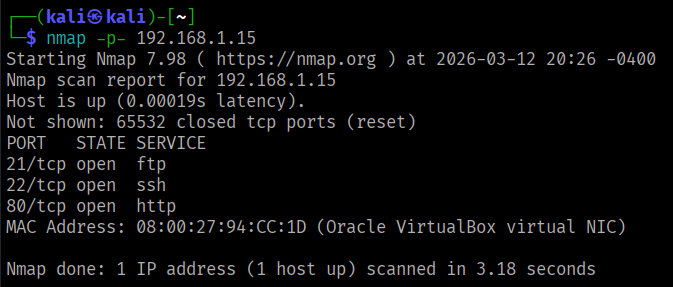
I performed a full port scan and identified three open ports on the target system.
Service Enumeration
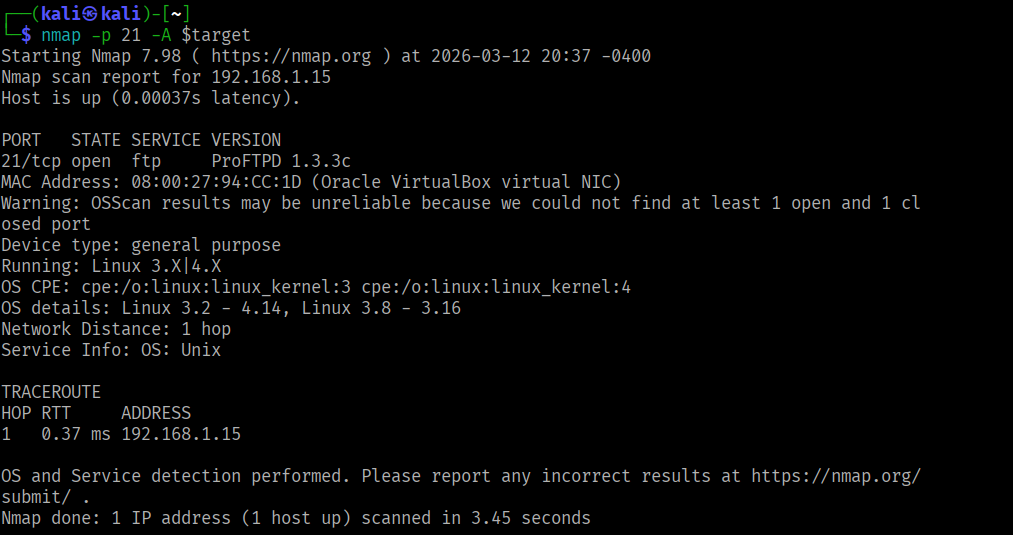
During enumeration, I identified the FTP service along with its version.
Exploitation
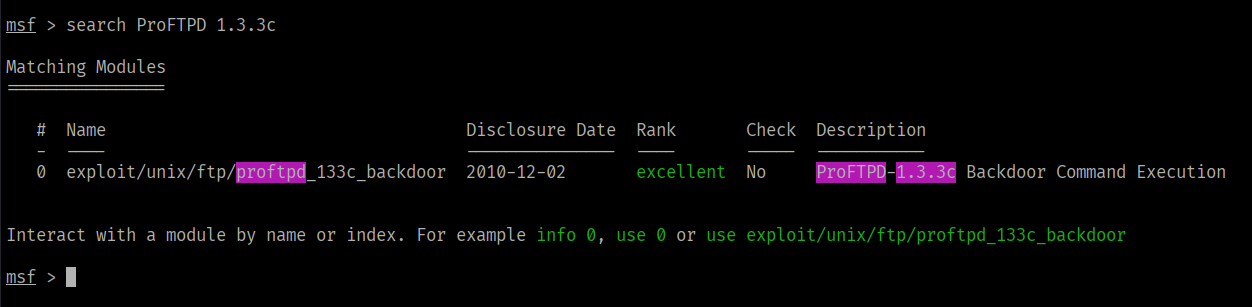
I searched for known exploits corresponding to the identified FTP version and found a relevant exploit module available in Metasploit.
Using the appropriate payload, I executed the exploit and successfully gained root access to the system.
Post-Exploitation
After obtaining a shell, I upgraded it to a fully interactive TTY using Python.
I then accessed the /etc/shadow file and extracted password hashes. The hashes were in SHA-512 Unix format.
Using john (John the Ripper), I cracked one of the hashes and recovered the credentials:
- Username:
marlinspike - Password:
marlinspike